Elevate Control
Triage, Prioritize and Respond Faster to Risky Users
Analysis finds that 8% of the workforce contribute to 80% of an organization’s security incidents. For Security Operations (SecOps), the behaviors of these high-risk users place considerable burdens on teams already overwhelmed defending against external threats. It’s time to flip this script!
Your Problem
Defending against external cyber threats is extremely difficult as attackers bypass your security technology using employees as the primary attack vector. 82% of breaches are due to the human element and adversaries are increasing their focus on targeting users, including a 2.5x increase in attacks against privileged users.
All of this adds up to security operations teams taking the role of cyber janitors, cleaning up after mistakes are made.
Our Solution
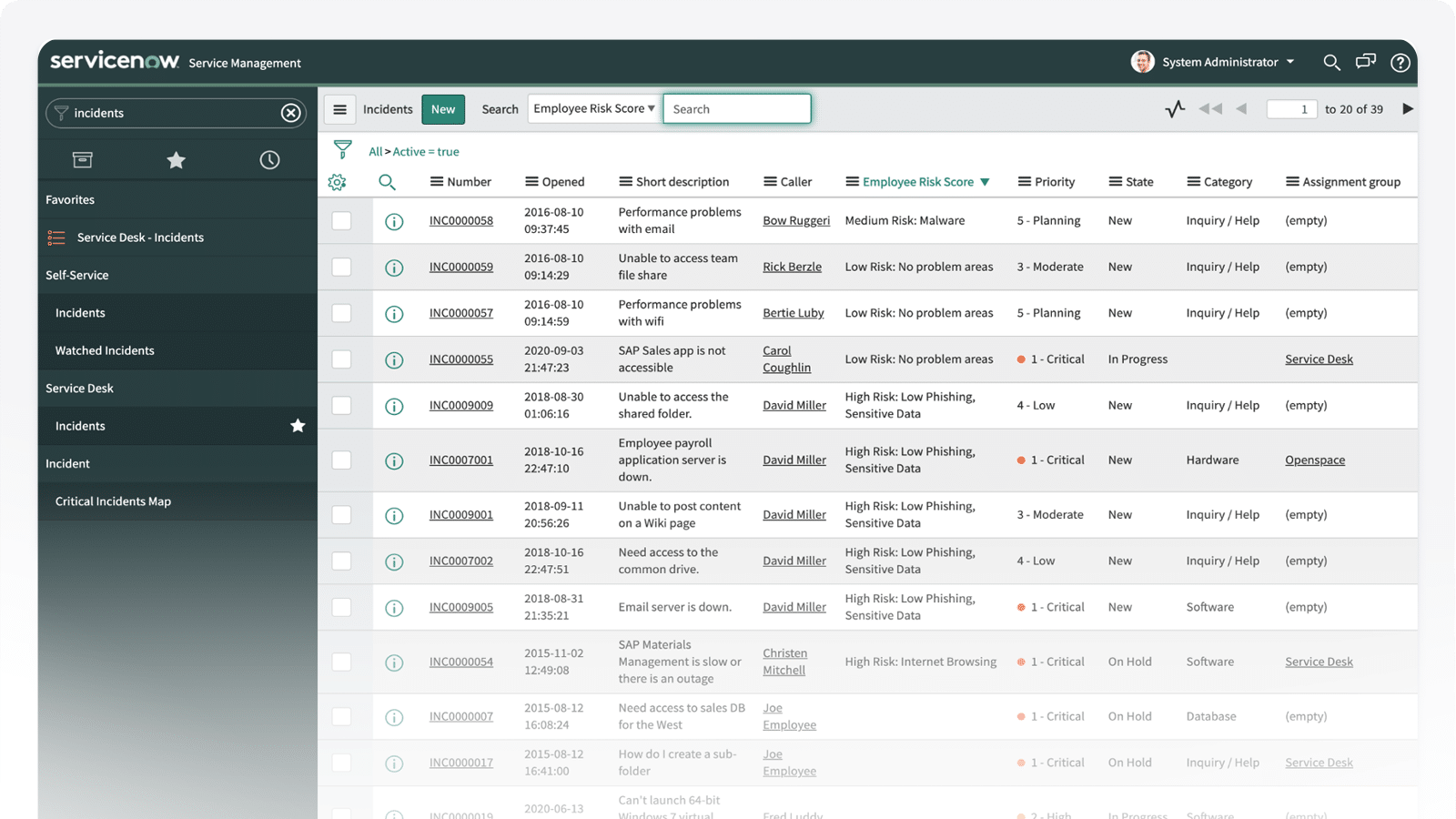
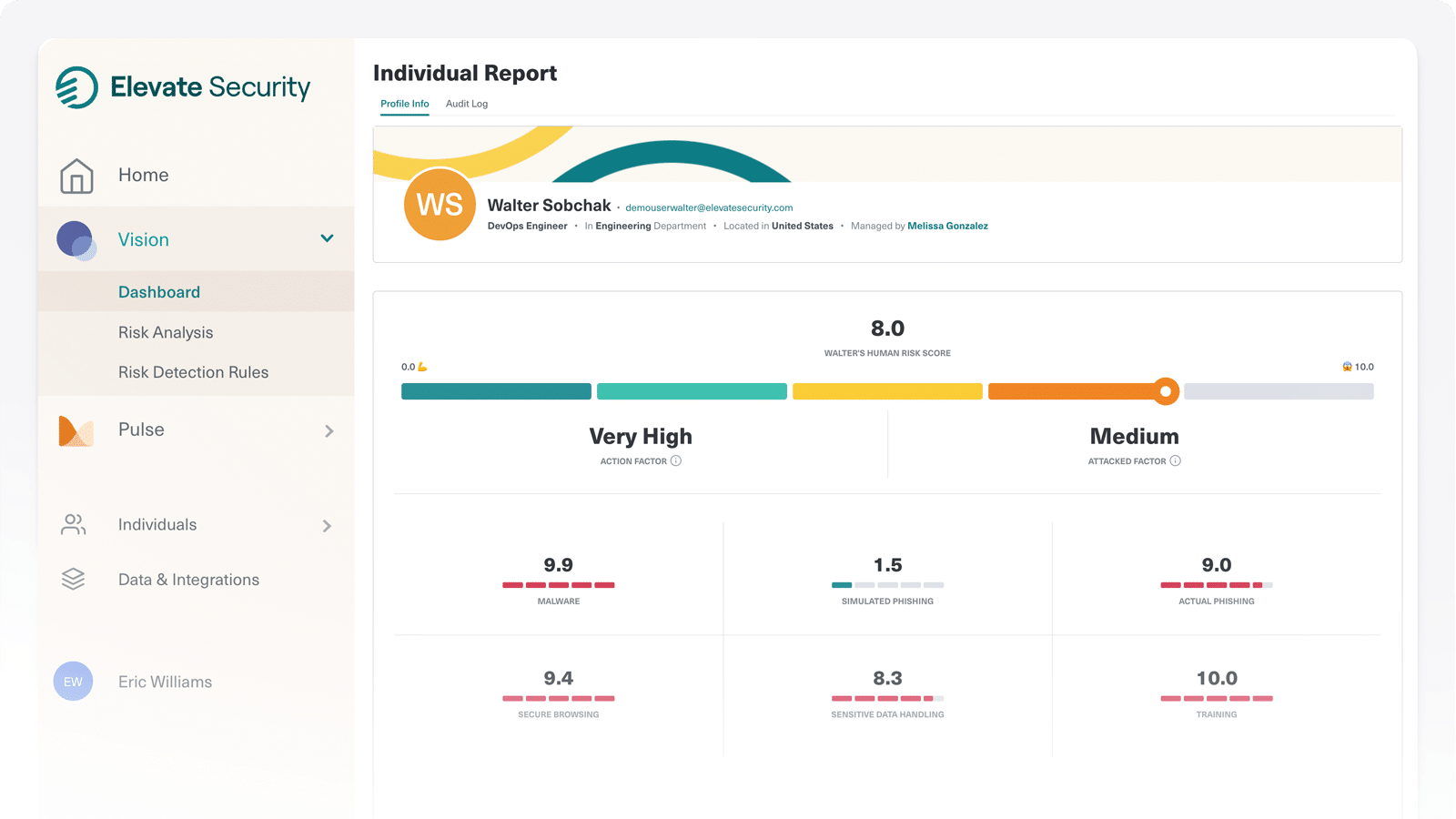
By pulling Elevate’s insights into SecOps tools such as SIEM, SOAR, and Case Management systems, analysts gain deeper visibility into user risk through detailed individual risk profiles allowing teams to quickly prioritize and better triage.
Security teams can take action on these insights by automating right-sized policy assignments in security control technologies. This allows organizations to address the 8% of users causing 80% of the incidents by placing stronger email security and web gateways controls on risky users, significantly decreasing the number of events to which they need to respond.
Latest News
Elevate and Cyentia Institute Earn "Top-Rated Session" status at RSA 2023
Reduce Incidents—Decrease SecOps Burden
Download the Product Brief
Download our product brief to learn more about managing workforce risk in security operations.
Automate Safeguards and Response to High-Risk Users
How Elevate Control Works
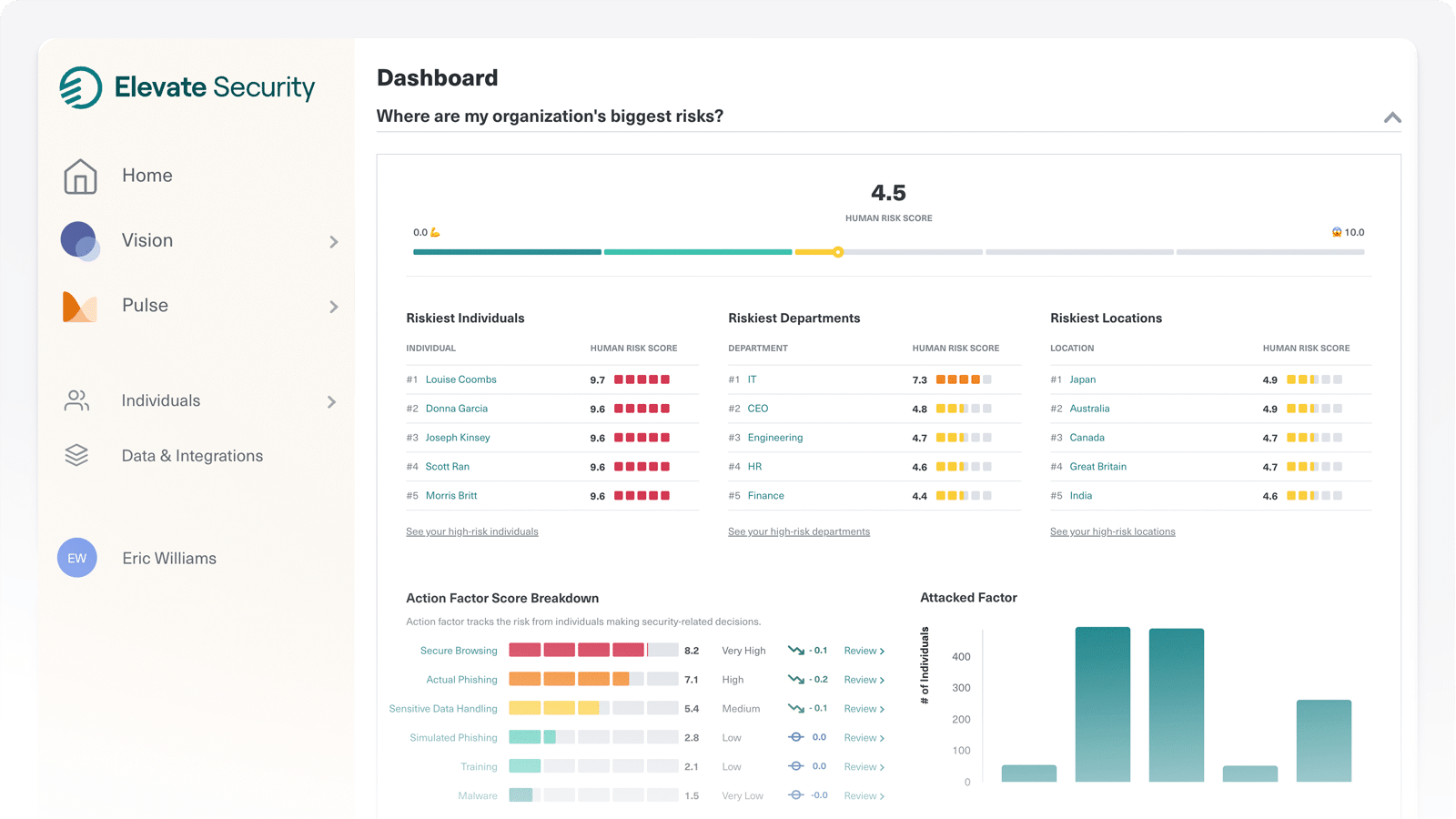
Elevate ingests and aggregates data from your enterprise to identify and score individual risk based on behaviors and attack history.
Elevate injects user risk data into Security Operations tooling to accelerate and prioritize incident triage and response, enable better analyst decision making, and automate right sized control policies for your riskiest users.
Deepen Security Intelligence
Ingest user risk data into your SIEM for stronger analysis of behaviors, patterns and historical risks.
Automate Controls
Use customizable playbooks to automatically apply stricter email, web and endpoint controls.
Speed Incident Triage and Response
Leverage user risk data to better triage and prioritize security events along with scope and blast radius.
Enable Better Decision Making
Integrating user risk data into case management workflows helps analysts make smarter decisions when handling cases and service requests.
Gain Visibility and Control of Your Riskiest Users
By operationalizing workforce risk data into your Security Operations policies, tooling, and controls automation, you'll free up resources to fight real adversaries, strengthen workforce safeguards, and improve response efficiencies.