Better Decisions
Authenticate User Risk during Identity and Access
One-Size-Fits-All Never Does.
Map Access to User Risk.
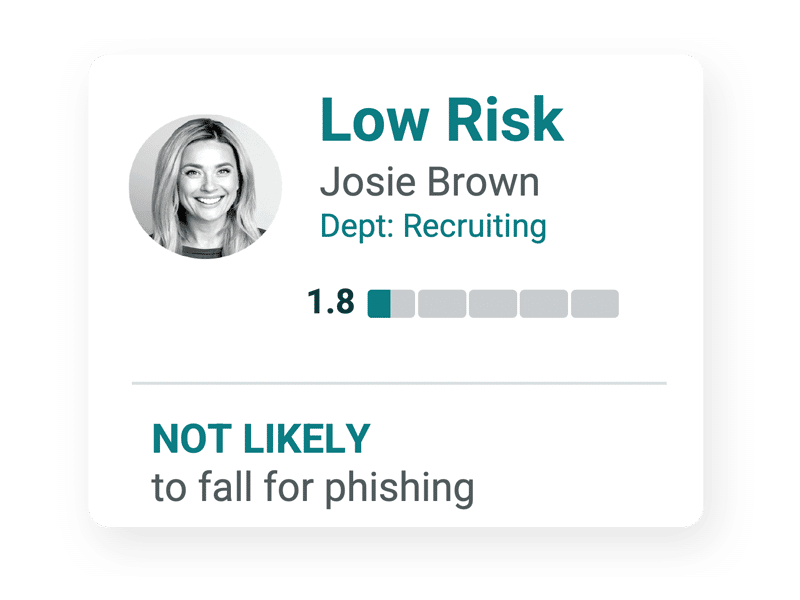
Offering the same access policies to every worker ignores the variety of risks each individual represents. Elevate partitions users by risk, allowing you to safely balance security and productivity, refine authentication and authorization decision-making, and move beyond a one-size-fits-all approach.
Partition User Risk
Elevate partitions users into specific risk groups based on individual risk profile. Elevate integrates directly with Microsoft Active Directory and other 3rd party tools to continuously update individual user partitioning as risks evolve. For example, dev/ops engineers with rising malware risk factors might be partitioned into a risk group entitled, ‘High Risk - Malware - Engineers’.

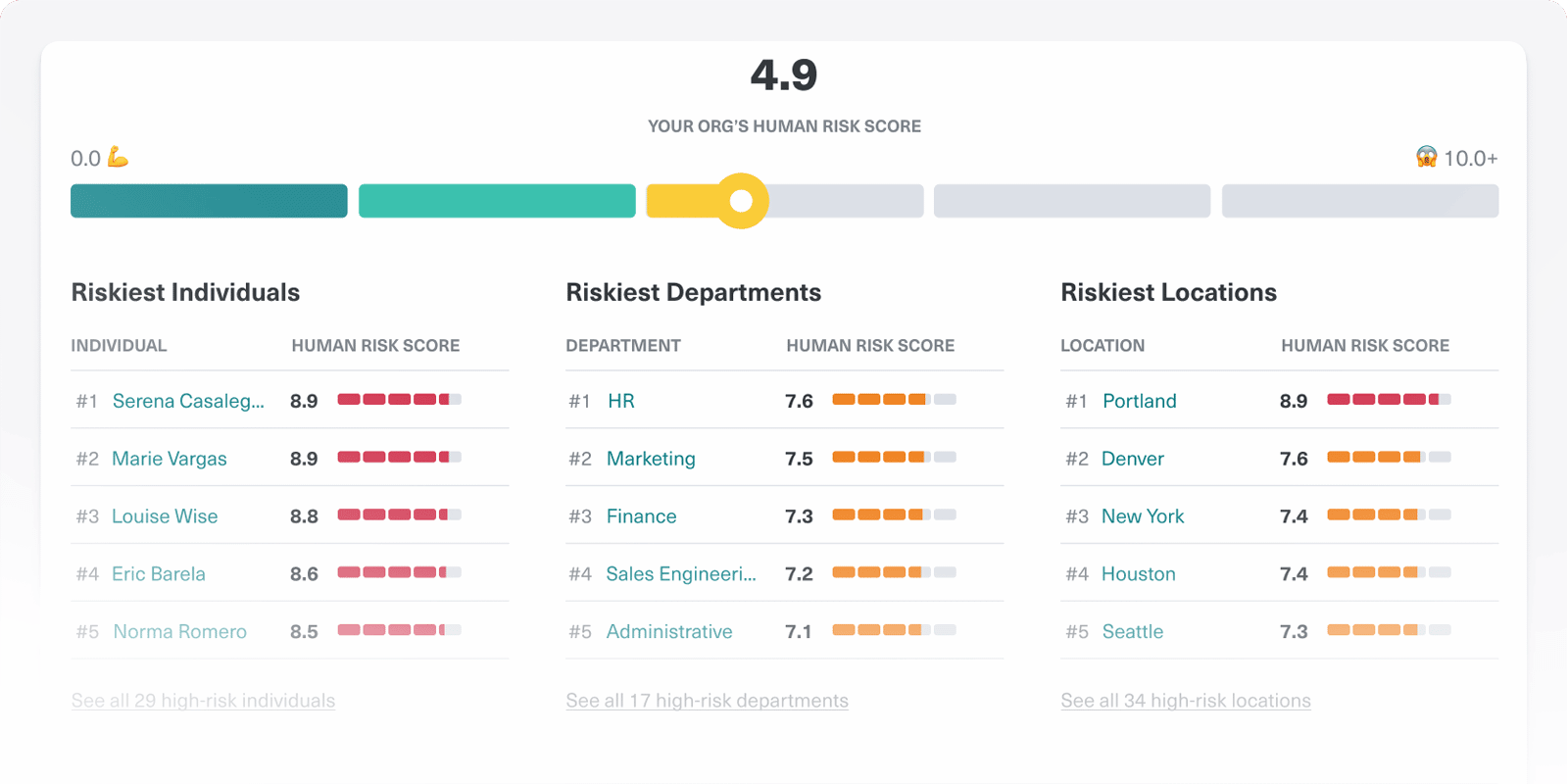
Executive
Elevate dashboards enable senior decision makers to instantly comprehend organizational risk, track the effectiveness of improvement programs over time, and communicate risk posture to the board and other stakeholders in simple, easily understood business terms. Benchmark organization risk performance against industries and peers. Align the organization, and incorporate internal workforce cyber risk into GRC initiatives. Drive compensation decisions based on security performance for truly transformational change.