Zscaler x Elevate Security
Enhance Your Identity and Access Management / SASE Strategy with Individualized Risk Data


Better Together
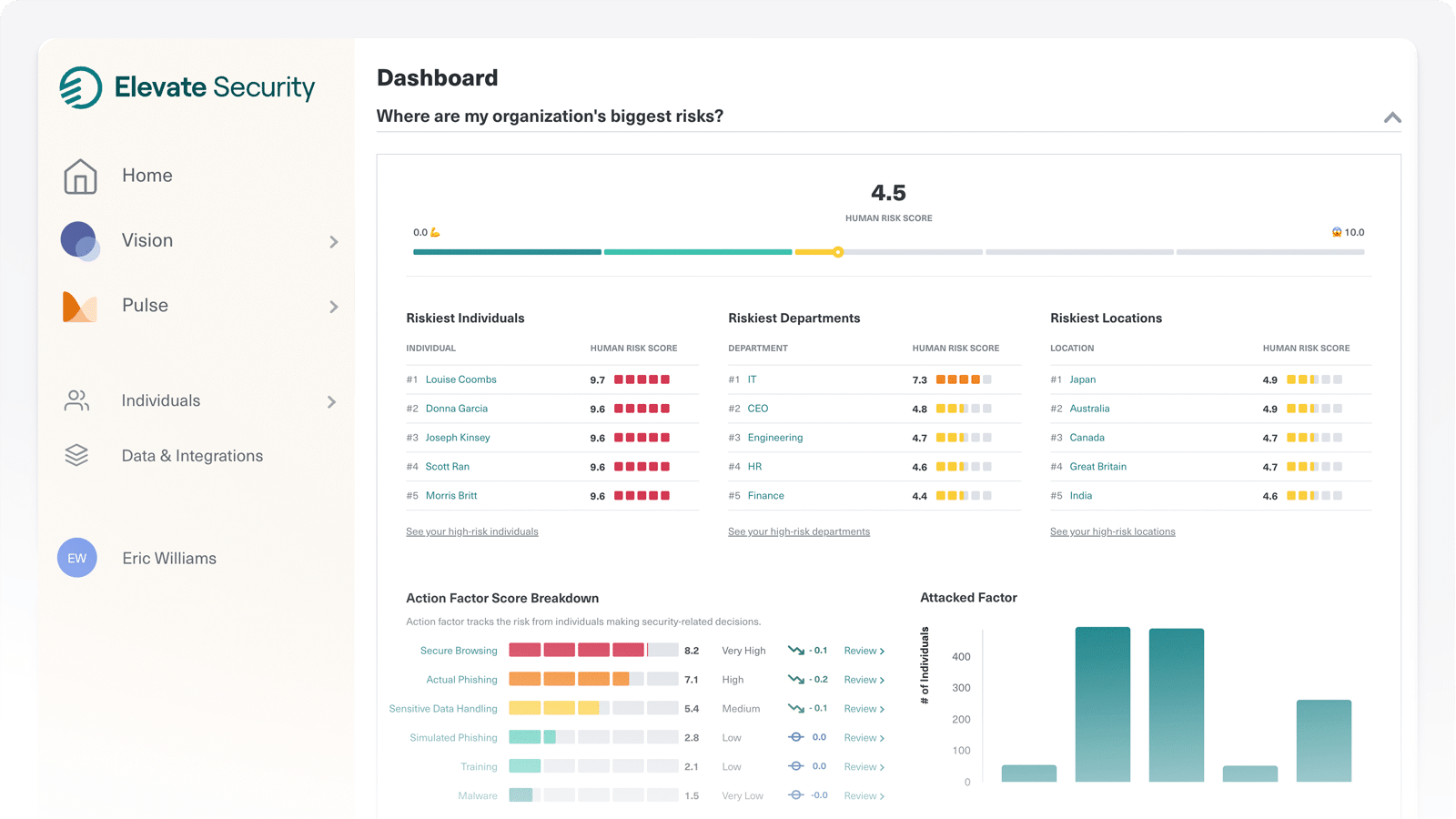
Data is pushed from Zscaler Internet Access (ZIA) using Cloud Nanolog Streaming Service (NSS) in real-time to the Elevate Security Platform. Elevate Security’s proprietary data science models automatically quantify the risk level of each individual in a credit-like risk score based on each individual’s behavior, decisions, data handling, and attack history.
Type
Integration
Software
Data Directionality
Into Elevate Security
Supported By
Elevate Security
Key Features of the Integration
Increase the effectiveness of ZTNA and SASE strategies with 360-degree visibility and intelligence into your workforce risk across threats such as ransomware, phishing, and malware. Make better security decisions and automate responses without burdening your SOC.
Quantified Risk Feed
Provides a holistic view into your workforce risk based on individual behaviors, decisions, data handling, and attack history.
Out-Of-The-Box and Customizable Playbooks
Enables you to automate tailored responses to each individual's risk levels.
Dynamic Security Controls
Continuously and instantaneously use the systems you have in place to protect people at computer speed.
The Problem
According to Forrester, 59% of security leaders recognize the need for a more holistic insider risk management program as part of their Zero Trust Strategy. Security leaders are challenged to protect higher-risk users, reduce the probability of a breach through proactive scaled responses, and maintain workforce productivity without adding additional burdens to security operations teams.
The Solution
Elevate Security & Zscaler — An Integrated Solution
Together, Zscaler and Elevate increase the effectiveness of Zero Trust Network Access (ZTNA) and SASE strategies by adding user risk to existing identity traits. Elevate collects user information, device data, and employee behavior indicators across many vectors, including email security, Endpoint Detection and Response (EDR), web security, Security Information and Event Management (SIEM) tools, and other technologies, including Zscaler. With this information, automated conditional policies can better protect users, requiring Multi-Factor Authentication (MFA), limiting access to those on an approved device, limiting web access, and even driving specialized training and feedback.
Leverage Zscaler’s high-resolution telemetry to gain deep actionable insights and attain a robust security posture infused with additional identity meta-data.
Download the Partner Brief
Download our partner brief to learn more about this integration.
Better Together
Data is pushed from Zscaler Internet Access (ZIA) using Cloud Nanolog Streaming Service (NSS) in real-time to the Elevate Security Platform. Elevate Security’s proprietary data science models automatically quantify the risk level of each individual in a credit-like risk score based on each individual’s behavior, decisions, data handling, and attack history. Leveraging Zscaler’s high-resolution telemetry along with Elevate’s out-of-the-box and customizable playbooks, security teams can respond to user-based risks in near real-time with tailored responses in identity management and governance technologies based on everyone’s risk levels.
For example, a developer with access to sensitive source control exhibiting other characteristics of account take-over can have their access modified, be required to present authentication factors that cannot be easily taken over such as hardware tokens, and have their existing sessions revoked - severely limiting an adversary’s ability to achieve persistence. These decisions can be made on an individual basis, or to groups of employees as needed to appropriately manage the risk to critical data and systems without preventing employees from doing their jobs.