CrossCountry Consulting x Elevate Security
Understanding Real-World Adversary Attack Patterns

CrossCountry and Elevate: Better Together
In a technology-overload world, people still matter. Elevate Security and CrossCountry Consulting are working together to tackle the people side of cyber: revealing the riskiest user behaviors. Making sense of exactly how adversaries attack. And helping business executives understand the real-world risks their companies face.
Type
Value-Add Partner
Company
About
A trusted business advisory firm that partners collaboratively with clients to navigate complex and pressing business challenges in order to improve operations, minimize risks and enable future growth.
Key Features of the Partnership
Elevate and CrossCountry are bringing together Elevate’s unique insights into employee risk with CrossCountry’s distinctive understanding of real-world adversary attack patterns – via Icebreaker, an elite offensive security brand that delivers adversary simulations for the world’s pre-eminent corporations. And we are integrating Elevate’s technology platforms and data with CrossCountry’s strategic consulting services to help companies holistically outpace human risk: balancing and harmonizing people, process, and technology.
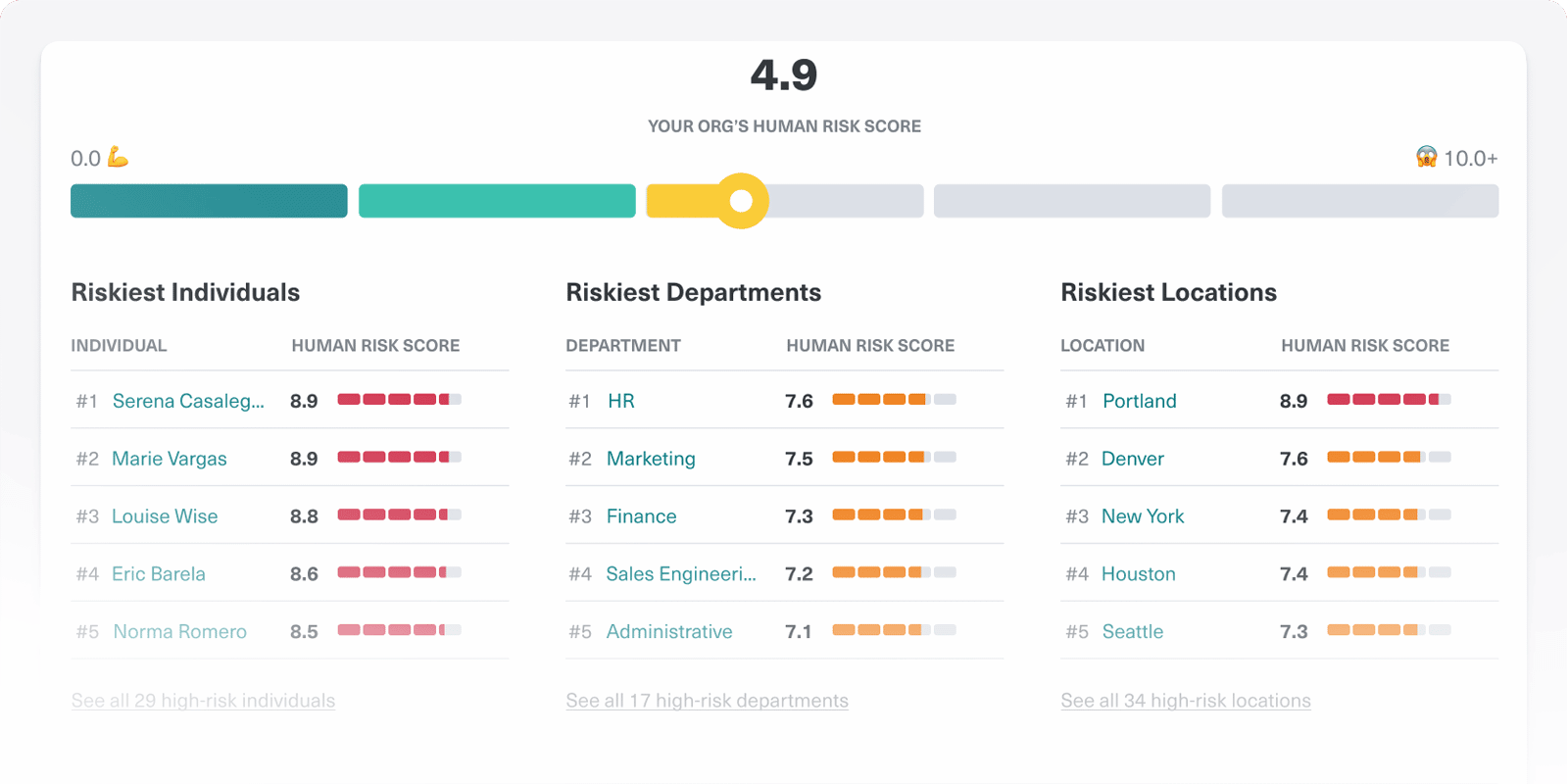
Quantified Risk Feed
Provides a holistic view into your workforce risk based on individual behaviors, decisions, data handling, and attack history.
Dynamic Trust Protections
Automated adaptive access policies that are highly tuned to the needs of each individual to protect people at computer speed.
Out-Of-The-Box and Customizable Playbooks
Enables you to automate tailored responses to each individual's risk levels.
Deal Registration Form
Register any deal over $100,000 by using the "Register Deal" button.
Benefits of the Partnership
CrossCountry and Elevate are helping companies transform how they:
Understand, Prioritize, and Talk About Risk
Re-Think Digital Identities
By fusing Elevate’s data into next-generation identity management strategies, architectures, and blueprints designed by CrossCountry security architects.
Design, Build, and Operate
Complete human risk programs that wrap fit-for-purpose processes and procedures around Elevate’s rich user data – all to help business and security leaders outpace insider threats.