Booz Allen
Dynamic Cyber Trust


Booz Allen and Elevate: Better Together
Booz Allen partners with Elevate Security to transform your Zero Trust strategy. Confidently establish Dynamic Cyber Trust with a deep understanding of your workforce risk by identifying and quantifying your riskiest users and automatically preventing your next security incident.
Type
Value-Add Partner
Company
About
Consulting firm with expertise in analytics, digital, engineering, and cyber, helping businesses, government, and military organizations transform.
Solution Brief
Download the Solution Brief
Key Features of the Partnership
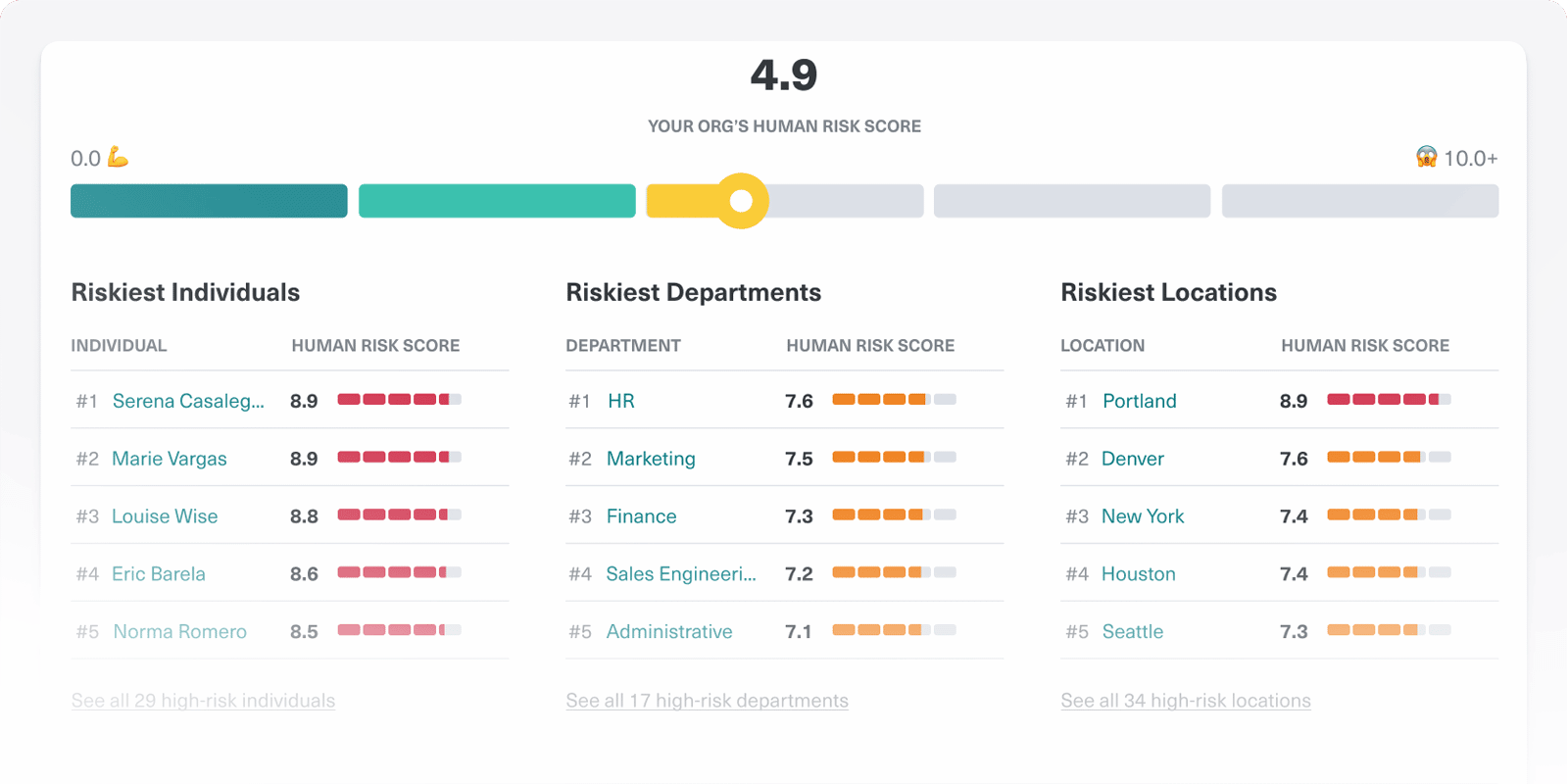
Booz Allen’s Dynamic Cyber Trust builds on core concepts of the emergent cybersecurity framework, Zero Trust, with human risk assessments and employee cyber behavior analysis. This strategic and predictive approach to organizational cybersecurity eliminates implicit trust, continuously validates every stage of digital interaction, and provides transparent and measurable human-centric feedback – through gamification – to reduce security gaps over time. Whereas Zero Trust keeps organizations safe today, Booz Allen’s world class consulting expertise powers a Dynamic Cyber Trust solution to drive continuously increased levels of security for tomorrow in the face of evolving threats.
Quantified Risk Feed
Provides a holistic view into your workforce risk based on individual behaviors, decisions, data handling, and attack history.
Dynamic Trust Protections
Automated adaptive access policies that are highly tuned to the needs of each individual to protect people at computer speed.
Out-Of-The-Box and Customizable Playbooks
Enables you to automate tailored responses to each individual's risk levels.
Deal Registration Form
Register any deal over $100,000 by using the "Register Deal" button.
Benefits of the Partnership
Build a more holistic insider risk management program for your Zero Trust strategy. Gain a deep understanding of your workforce risk, helping you to make better decisions and automatically tailor security safeguards to the individual risk level of each user.
Powerful Insights
Deep understanding of workforce risk based on individual security decisions pinpointing your organization’s high-risk workers. Identify issues, orchestrate action, and remediate workforce risk before the next incident strikes.
Better Decisions
Extract hidden value from your cyber-tech stack by bridging silos, normalizing data, and analyzing disparate risk signals across your enterprise to make smarter organizational decisions based on individual risk levels.