What Is Human Attack Surface Management?
The Elevate Security platform provides enterprises deep visibility into human risk and automates tailored security controls, personalized feedback, and policies to reduce incidents.
The overwhelming majority of security incidents are caused by human error. It's time to reduce the frequency and impact of these incidents.
It's What Your Employees Do, Not What They Know, That Matters
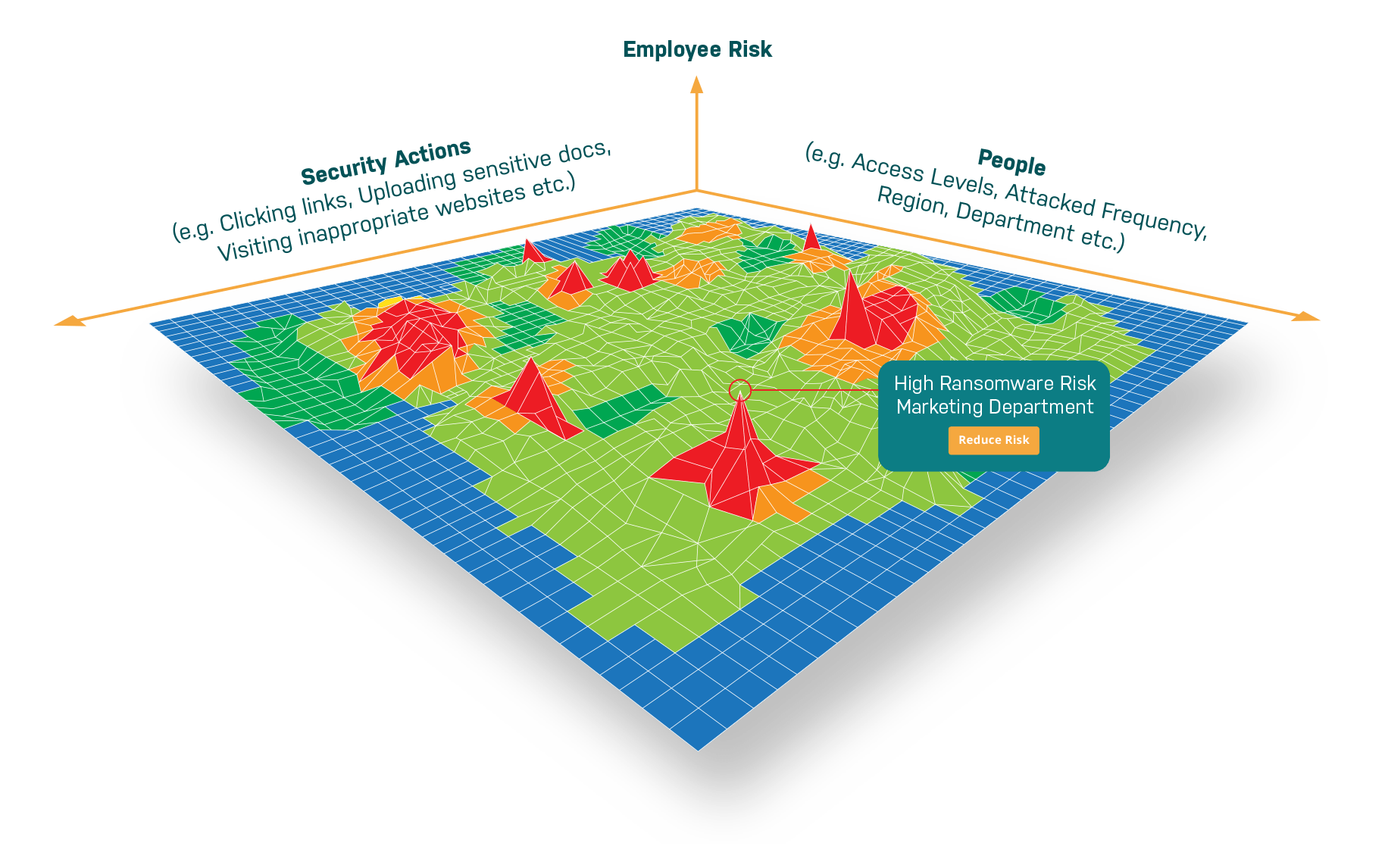
Every decision that your employees make - good and bad - impacts your enterprise's security posture. It's time to start understanding your human attack surface which is defined as the sum total of people's actions, access, and security controls that impact and organization's risk.
Human Attack Surface Management delivers two key benefits to your security team:
Gain valuable insights into the human risks your organization faces
Take action confidently to reduce your human risk
Most companies lack a real understanding of the risks their end users present. Human Attack Surface Management will give you a deeper understanding of each and every employee, contractor or supplier – especially the riskiest ones. You gain visibility at the individual, group, department, or regional level. Then Human Attack Surface Management helps you manage the controls that help to mitigate and shrink your potential attack surface.
Human attack surface management addresses specific threats with specific remediations
Visibility and Context for Your Insider Risk
Visibility into your people and their activity is the foundation of human attack surface management. It provides the context to make informed decisions. Absent real data, security teams have been forced to use 'security and awareness training' as a crutch. Whether or not an employee flunked a security quiz or failed a phishing test is not an actual measure of risk.
The human attack surface can be measured using the tools and data you already have. The key components are:
- People - Directory services and HR platforms
- Actions - Email security gateways (phishing), web gateways (internet browsing behaviors), identity solutions (password security), endpoint protections (malware), data loss prevention tools (data handling), etc.
- Access - Access management, directory services, Application RBAC
- Security Controls - Already used in the tools above
Proactively Control the Human Attack Surface
What is measured, must be managed. With trusted visibility into each individual user’s actions, access and security controls, we have a full picture of their risk. Some employees act securely while others are more risky. You can reduce friction in the organization but taking targeted, tailored actions instead of one-size-fits-all controls. Some ideas include:
- Automating personalized and adaptive policy orchestration in tools to add safety nets for higher risk employees
- Zero Trust implementations using risk data around authentication or access decisions
- Providing real-time feedback to the employee on their security performance
- Providing tooling to your analyst functions that approve things such as access or software downloads
- Tailoring software deployments which have higher costs or friction to your most risky employees
- Security investment assessments to determine efficacy of rollouts and their impacts to your employees